- cross-posted to:
- [email protected]
- [email protected]
- [email protected]
- cross-posted to:
- [email protected]
- [email protected]
- [email protected]
remember, kids - if you see something,
…hit it with a port mirrored packet sniffer.
I didn’t even hook ours up to the WiFi. For our use, there is no conceivable advantage and this is the downside.
Now where can we get this port mirrored packet sniffer? But seriously, how do you do this?
if your switch gear will mirror traffic, then push the traffic to a switchport with a PC running software like wireshark/tshark/tcpdump or your fav. packet sniffer of choice. different setups (integrated wireless, fibre, etc) will require various configuations to packet capture properly, but you can always find a way of observing traffic - even if you have to use an old hub (not a switch) as a last resort and just flood the traffic to your monitoring device.
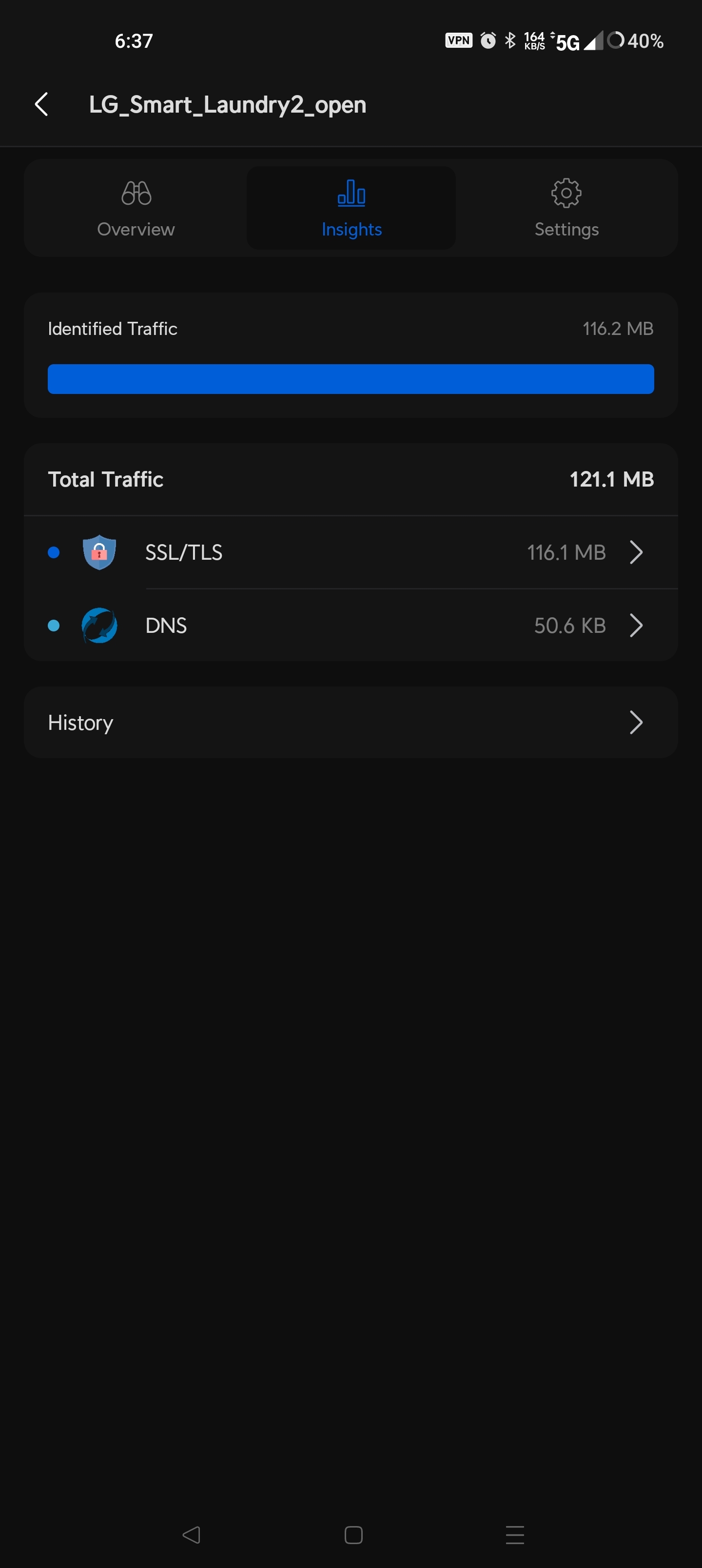
once you have a packet trace, things get fun. if the traffic is in the clear (not encrypted) you get all the goods. if its encrypted (and you cant man-in-the-middle attack the crypto session) then, at the very least, you get patterns, timings, IP endpoints, etc…
on higher end switch and router gear (and some open source consumer routers) its pretty easy to sniff traffic and a great learning experience, not to mention the ability to monitor traffic gives you insight into what devices are doing “things” on your network. highly recommended playing with it on a spare laptop to get some experience with it.
Intrusion Detection / Protection Systems often make use of this type of traffic visibility. so do ISPs (and others) for various purposes, of which some usecases are highly privacy unfriendly.
edit: fixed a few obvious typos and added the IDS stuff.
Remember when washing machines were controlled by rotating cams and microswitches?
Why the hell does a washing machine have a network connection?
Eh, was going to learn more, but basically it’s the tweet plus summary of silly answers he got and nothing more.
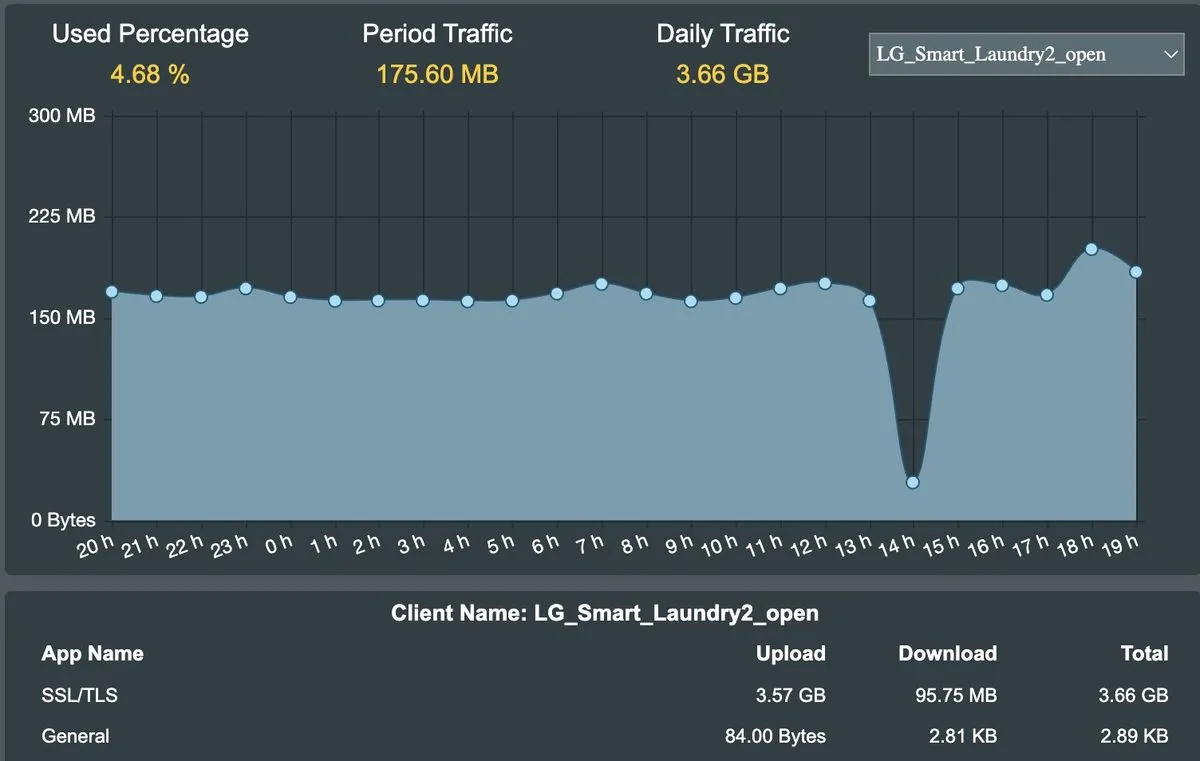
My suspicion is that maybe it got compromised and used for DDoS botnet.
Even if that’s the case, it’s a good reason to not connect it. If lg doesn’t secure their device well enough then they should not use it.
Oh I don’t argue about that. I personally try to avoid anything “smart” primarily for privacy concerns.
I was just curious what the cause was. In another comment someone suggested that the washing machine was eavesdropping which would be consistent with usage was mostly uploading, but I think 5.7GB would be too much data, unless it was uncompressed.
I’d bet it is uncompressed. There is probably the cheapest slowest processor in there that they could get away with.
What do they care if they eat up your bandwidth?
Then can easily compress it once it arrives wherever it’s going.
My LG washer is not sending that much data. Maybe the guy is blocking the phone home and it got in a loop trying to call home.